TheHarvester
I’m going to present this tool in two ways to show simultaneously how cool this utility is and the slightly less impressive way it is actually done:
What appears to happen:
- Type in a username, receive a list of sites that user exists as a member.
- Type in a company name and get a list of people who likely worked or still work there
- What is this magic!?
What actually happens:
- Web scraping!
That being said, TheHarvester is a really cool tool and I’ll cover what I think is it’s best feature – LinkedIn user scraping.
Using TheHarvester
Head on over to GitHub and grab the utility here: https://github.com/laramies/theHarvester
Setup is pretty simple, install any missing dependencies, chmod the file, and kick it off. You will see a nice help output and some examples.
One of the ‘coolest’ features, in my mind, is how it scrapes LinkedIn for users. You put in the ‘number’ of results you want, the ‘company name’ – this represents what to look for in the ‘current/former employee of’ part of LinkedIn, and then how to output it! Let’s grab the first 200 ’employees’ of google it can find!
./TheHarvester.py -b linkedin -l 200 -d "Google, Inc."
That’s all there is to it! This is very powerful and very simple to use 🙂
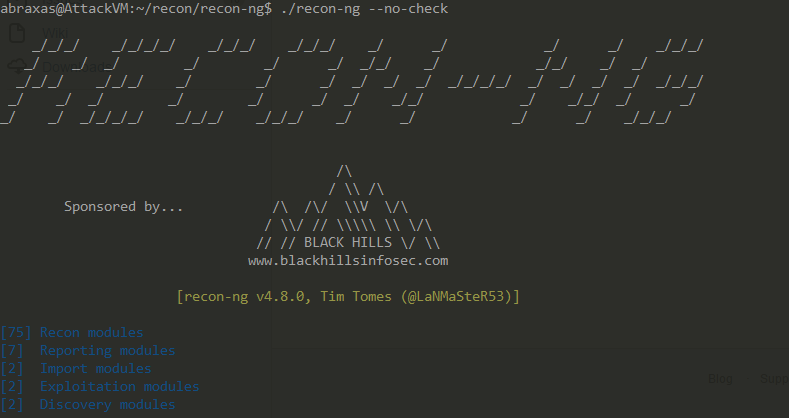
Recon-ng
Recon-ng is a far more expansive project than TheHarvester which offers many more features and tools. Whereas TheHarvester is a script which quickly does something, Recon-ng builds its own database and has many more modules, it even comes with a nice CLI to query the database and/or script actions to do on each item in different tables of the database.
The project itself can be found here: https://bitbucket.org/LaNMaSteR53/recon-ng
Once loaded, you’re greeted with a Metasploit-like interface with a similar navigation and ‘show’ interface:
Typing show modules provides a list of the many modules available. Let’s say you have a series of names or usernames of a company and you want to see if any of them have any GitHub projects (perhaps sysadmins hosting tools they shouldn’t be). You can import those users to the contacts table and then run the following module (after adding your API key):
load recon/profiles-contacts/github_users
Voila! A quick, scriptable item which will allow you as a pentester or defender to quickly enumerate users/profiles and see if they might be hosting interesting content on GitHub!