
This series is about setting up a recon machine in the cloud, using some basic tools, and diving in to the recon process! As I move my career in to the security space I want to document my process. Part of this involves testing various utilities and trying my hand at automating some of the common tasks. These posts are going to cover my experiences.
The Setup
I am hosting my machine as a VM in the Azure cloud as a part of my BizSpark membership. Incidentally, this I am also hosting this blog there! I chose Ubuntu as the distro as I am more familiar with it and it’s packages than other linux distros. I set this up with 4GB of RAM and 2 procs – everything else is pretty standard.
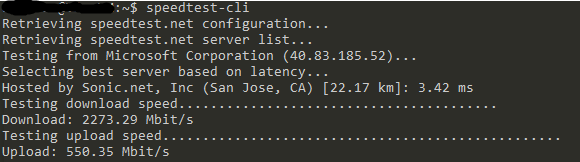
The first thing I did was to get everything up to date, set some iptables rules setup an entry point for scp/ssh and tested that everything was working. Also checked the connection which clocked in at at solid 2273mb down and 550mb up…so that was cool.
Recon 101
I will be organizing this discussion of recon in to two types – passive and active. Passive is zero-touch, meaning that the scanning/recon never touches client infrastructure. For instance, this does not involve scraping their website for target email addresses but, instead, searching 3rd parties for that information. This type of recon typically is totally undetectable by the target. The second kind of recon is ‘active’ which does actually involve touching target systems – such as crawling or enumerating pages/subdomains of the targets site. This kind of recon can be noticed or logged by the target. As a caution, if done improperly, this can result in denial-of-service style attacks. So, in the words of Zoz, don’t fuck it up!
There are a few reasons to do both passive and active recon. If doing a pentest, you can identify large parts of the attack surface with these tools. Such things include email addresses for phishing, usernames, subdomains, IP addresses and more. This type of activity can also be used defensively to determine your public footprint. Used this way it finds systems misconfigured to have public access, internal hostnames and more.
What remains of this blog post is not presented in a ‘you should absolutely do things in this way’ order, but it is intended provide a list of the major recon tasks, how to do them, some analysis of what to look for, building automation, and then a brief dive in to mass recon!
In the next posts we will look in to a few of the basic tools, how to handle the output, and start process of automating these tasks.
Part 2 of the article covers Fierce, nslookup, and dig. Part 3 is not yet available.